Meng Su explains how Dridex works and how it communicates with its C&C server.
A descendant of Cridex, Dridex was first written about a little less than a year ago, by
S21sec
and
abuse.ch
. Since then, Dridex has evolved to become one of the more prevalent banking trojans.
Dridex often spreads via attachments to spam messages, for instance as the payload to malicious
Office
macros, which a user is tricked into activating.
Today, we publish an analysis of Dridex by
Tencent
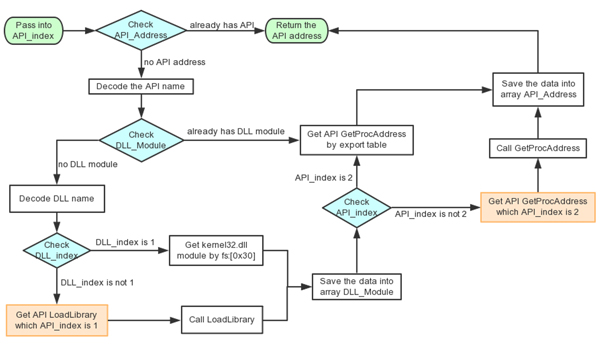
researcher Meng Su. In the paper she looks at how Dridex obtains the
Windows
APIs it uses and how it then sends information on the system to a command and control server.
You can read the paper
here
in HTML format or
here
as a PDF.
Posted on 13 July 2015 by
Martijn Grooten
Leave a Reply