Obfuscation in malware has long frustrated analysis, and obfuscation at the compiler level, such as opaque predicates and control flow flattening, has been particularly challenging. One group that has been using this kind of obfuscation is APT10, an APT group made famous through a 2018
indictment
by the US government in which two Chinese individuals were charged.
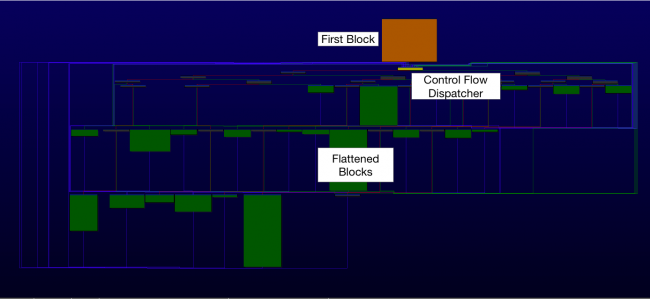
Function obfuscated with control flow flattening.
At VB2019 in London,
Carbon Black r
esearcher Takahiro Haruyama presented a paper on defeating compiler-level obfuscations used by APT10, in particular in the ANEL/UpperCut RAT used mainly against targets in Japan. In conjunction with this paper, Takahiro also released a
tool
that can aid analysis in
IDA Pro
.
Today we publish Takahiro’s paper in both
HTML
and
PDF
format as well as the recording of his VB2019 presentation.
Have you carried out research that furthers our understanding of the threat landscape? Have you discovered a technique that helps in the analysis of malware?
The
Call for Papers
for VB2020 in Dublin is open until
15 March
– submit a proposal now for a chance to make it onto the programme of one of the most international threat intelligence conferences!

Leave a Reply