Trickbot, first
reported
a year ago by
Malwarebytes
researcher Jérôme Segura as the successor of Dyre/Dyreza, has become perhaps the most important banking trojan of 2017. It is known for its regular updates, with
its use of SMB
for lateral movement particularly noteworthy.
Symantec
‘s Director of Threat Research
Andrew Brandt
is one of many security researchers who keeps a close eye on Trickbot. In particular, he has been focusing on its command-and-control communication over TLS-encrypted channels, by using a tool that allows him to perform man-in-the-middle decryption. He presented his findings as a
last-minute paper
at VB2017.
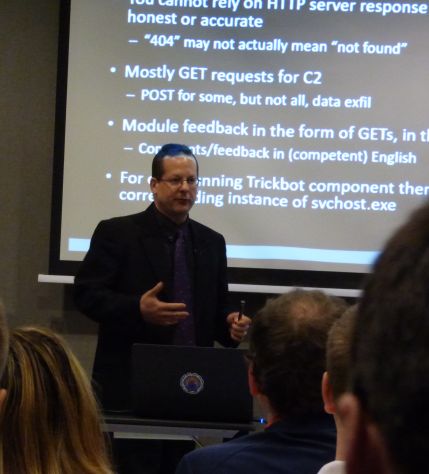
Andrew Brandt presenting his paper ‘Turning Trickbot: decoding an encrypted command-and-control channel’ at VB2017, Madrid.
Today, we have uploaded the recording of Andrew’s presentation to our
YouTube
channel. We have also published his slides (
pdf
), for those who want to study the many technical details of Andrew’s talk a bit more carefully.
Leave a Reply