When, a few years ago, a friend and I were
analysing
a rather large botnet and we saw some network traffic indicating that it was engaged in Bitcoin mining, we felt rather disappointed: using malware to mine for cryptocurrencies is about as basic as it gets. It is the digital equivalent of breaking into someone’s house, stealing all their books and furniture, and then burning them to use as fuel.
That was four years ago, but miners continue to thrive:
Kaspersky
researchers
say
they have seen 1.65 million infections involving mining software in 2017 alone, while
ESET
writes
about how some malicious ads use JavaScript to mine cryptocurrencies in the browser.
Cryptocurrencies (or ‘crypto’, if you want to annoy the cryptography community) have seen huge increases in their value, but even at the current rates, why would someone use a compromised PC for mining purposes, when there are
Bitcoin farms
that use dedicated hardware to mine far more efficiently? Wouldn’t every calculating cybercriminal switch to the far more profitable ransomware instead, preferring hundreds of dollars (even if not every victim ends up paying) over mere pennies?
The probable answer lies in the global distribution of malware. Cybercriminals have discovered that a few hundred dollars is the ‘right’ amount for a ransom: enough to generate them a good income, yet affordable for most users who really want their files back. But this is only true for users living in Western countries, on Western incomes. And the Western world is not where the majority of malware infections exist.
In its State of Malware Report (
pdf
) from the beginning of this year,
Malwarebytes
writes that almost two-thirds of botnet detections are in Asia or Africa, compared with barely more than ten per cent of ransomware detections.
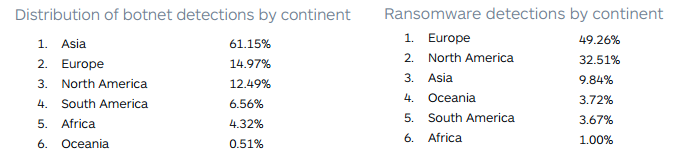
Source: Malwarebytes
.
The first stage of a malware infection is often a ‘loader’, whose sole task is to download the actual payload. A number of factors are taken into consideration when determining which malware to download, and geographic location is prominent among them. Thus the same malicious spam email can lead to ransomware in one country and to Bitcoin mining malware in another, where ransomware is not likely to yield sufficient gains.
As human beings, cybercriminals often don’t make fully rational decisions. But when it comes to using their botnets to mine for malware, there really is a simple explanation.
Leave a Reply