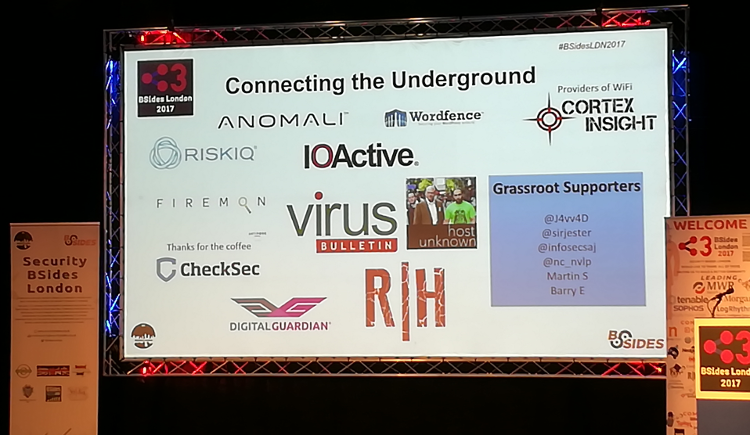
This month, for the first time in its 28-year history,
Virus Bulletin
became the sponsor of another industry conference:
BSides London
. I have to admit to having been more than a little proud to see the
VB
logo displayed on the screens in between sessions. Of course, I was also happy to see lots of people pick up the
VB2017
flyers that were distributed throughout the conference area, but most of all, I was thrilled to have
VB
contribute to such a great community event.
I attended the conference together with
VB
team members Péter Karsai, Scott James and Chris Stock; this blog post reflects all of our views.
One thing that I (and many others) noted was that, in more than one way, the audience was very diverse. Whatever your views on the need for diversity in security, diversity does broaden the talent pool. And companies are desperate to hire skilled researchers – in fact, several of the event’s sponsors, including non-security firms like
JP Morgan
and
Amazon
, were attending
BSides
with the explicit goal of recruiting new talent for their teams.
Indeed, the BSides’ ‘Rookie’ track is a great place to find such new talent. This track is dedicated to those who are relatively new either to the industry or to public speaking, offering them the opportunity to give short presentations, during the preparation for which they are mentored by industry veterans. While the goal of the track is for the presenters to learn, we also learned things there, for example on
malware analysis
and the implications of
IPv6
for security.
It was in this track that we saw Jelena Milosevic give a
short talk
(her “maiden presentation”) on building a user awareness programme, based on her experience of working as a hospital nurse. She will call on the same experience at VB2017, where she will
describe
the consequences of bad security in health care. (Jelena has also written a
Peerlyst
post
on the subject of awareness.)
As befits a hacking conference, several talks discussed hacking tools that may be useful for those engaged in pen-testing. One such
talk
discussed a £20 device, based on a
Raspberry Pi
, that when plugged into a
Windows
PC obtains a hashed password, attempts to crack it in the cloud and, if the password isn’t very strong, gives you access to the PC within 60 seconds.
It’s not just lack of desktop security that is an issue. Another
presentation
looked at
Alexa
‘s list of the one million most popular websites and their security. Depending on the colour of your hat, there is either a lot to be improved there, or these sites still provide a lot of opportunities.
Another interesting
talk
looked at building a search engine for data gathered from third-party data breaches and in doing so highlighted both the issues with building such a local database and with the lack of security in customer databases that leads to such breaches. One interesting take-away from the talk was that there are people who, in the ‘password hint’ field helpfully write ‘vpn password’ or ‘pos password’ to indicate where they have used the same password.
We also enjoyed a
presentation
on the use of truly anonymous credentials: the problem of someone authenticating as part of a certain group, without providing any clues as to which group member they are. Although the amount of maths involved may have been a little too ambitious for a 45-minute talk, it was interesting to see how cryptography provides a solution for this perhaps unusual scenario.
With no fewer than seven parallel tracks, there were many sessions that we were not able to attend. This included a number of workshops that really channel the BSides philosophy of there being no ‘attendees’, just
participants
. We had a great time participating and are already looking forward to next year’s event — or to one of the
many BSides events
that take place around the world.

Leave a Reply