Why buying ad space makes perfect sense for those wanting to spread malware.
Over the next few months, we will be sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added ‘Optimized mal-ops. Hack the ad network like a boss’ by Bromium researchers Vadim Kotov and Rahul Kashyap.
Malicious advertisements (‘malvertising’) go back more than a decade, yet in recent months we have seen a surge in these attacks, including the ‘
Kyle and Stan
‘ campaign, which affected
Yahoo
,
YouTube
and
Amazon
, among others, and the
campaign
that used ads bought at
DoubleClick
and
Zedo
to spread malware via the website of some Israeli newspapers.
This surge was predicted in Vadim Kotov and Rahul Kashyap’s VB2014 paper – the paper also explains why it makes sense for cybercriminals to turn to malvertising.
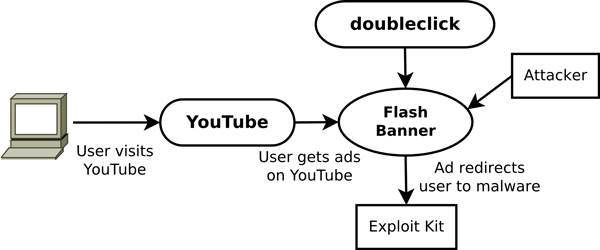
The paper includes a case study on malicious ads served on YouTube.
If a cybercriminal wants to spread malware, a common way to do so is by serving exploit kits on compromised websites that drop the malware onto the machines of vulnerable visitors. However, the attacker has little control over who visits the website, and has to depend on compromising the site in the first place.
So what if an attacker could just pay to serve malware on just about any popular website and even get to choose to which demographic the malware is being served? This is exactly how online advertising works and is the very reason why, unless you use tools that block trackers, most of the ads you will come across on websites you have never visited before are somewhat relevant to your browsing history.
The
Bromium
researchers show how the power of
Adobe Flash Player
makes
Flash
banners an ideal vector for serving malware, while the targeting of ads means that an attacker can even choose only to serve the ads to visitors using, say,
Internet Explorer
and
Windows XP
. In his presentation in Seattle, Vadim performed a demonstration in which he was easily able to hide the payload of a malicious advertisement in an innocent-looking PNG file.
You can read the paper
here
in HTML-format, or download it
here
as a PDF (no registration or subscription required). You can download the presentation slides
here
. We have also uploaded the presentation to our
YouTube
channel.
Last month, Rahul was
interviewed
by the
Risky Business
podcast on the findings of the paper.
Posted on 18 November 2014 by
Martijn Grooten
Leave a Reply