Researchers Vadim Kotov and Rahul Kashyap to discuss how advertisements are the new exploit kits.
In the weeks running up to
VB2014
(the 24th Virus Bulletin International Conference), we will look at some of the research that will be presented at the event. In the second of this series, we look at the paper ‘
Optimized mal-ops. Hack the ad network like a boss
‘, from Vadim Kotov and Rahul Kashyap, two researchers from Bromium.
“We conclude that ad networks could be leveraged to aid, or even be substituted for current exploit kits.” It is a slightly worrying conclusion that Vadim and Rahul draw in their paper – but they provide good arguments for it.
Exploit kits have been the scourge of the web for many years. Typically starting with a single line of inserted code, they probe for a number of vulnerabilities in the browser or its plug-ins and use this to drop malware onto the victim’s machine. Given the high proportion of Internet users that haven’t fully patched their systems, it is a successful way to spread malware.
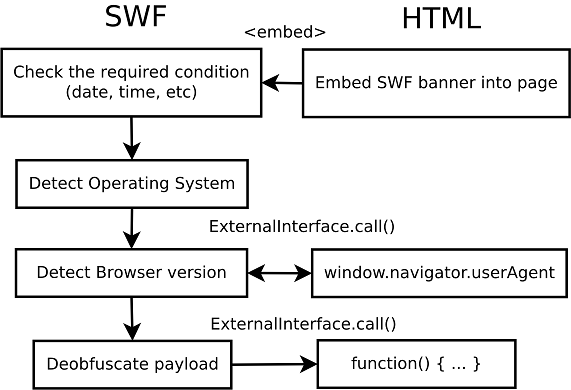
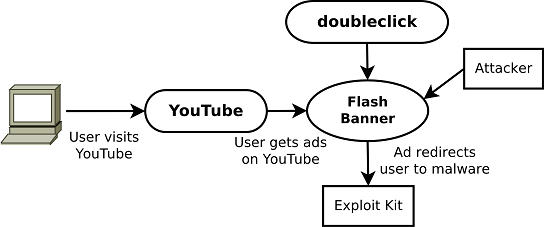
However, in order for exploit kits to do their work, a vulnerable website must first be infected, or the user must be enticed into clicking a malicious link. But by purchasing ad space, and using this to place malicious ads, attackers have discovered a cheap and effective way to get their malicious code to run inside the browser of many users. They can even tailor their advertisements to target specific languages, regions or even website subjects.
In their paper, Vadim and Rahul look at a case study of malicious ads served by
YouTube
(demonstrating that even top brands are battling against this threat), and also study the more general case of malicious Flash banners and how they are obfuscated from researchers, while still delivering malware. We learned last month that this is a serious problem – when researchers
found
that cybercriminals had purchased advertising space on
Yahoo
in order to serve the ‘Cryptowall’ ransomware.
Ideally, of course, advertising networks would block malicious ads as they are added to their systems. In their paper, the researchers explain why this is easier said than done: given the size of such networks, it would take a lot of time and resources – plus, technically, it’s difficult to block most malicious ads without a certain percentage of false positives.
You can now
register
for VB2014. And if you have some research that you want to share with the security community, why not
submit an abstract
to fill one of the seven remaining ‘last-minute’ presentation slots?
Posted on 15 August 2014 by
Martijn Grooten
Leave a Reply