FireEye researchers show a large attack vector for Apple’s mobile operating system.
In the weeks running up to VB2014 (the 24th Virus Bulletin International Conference), we are looking at some of the research that will be presented at the event. Today, we look at the paper ‘
Apple without a shell – iOS under targeted attack
‘, by FireEye researchers Tao Wei, Min Zheng, Hui Xue and Dawn Song.
Whether you believe its success is because of superior products or merely superior marketing campaigns,
Apple
has once again made the headlines with the announcement of a new product. The
Apple Watch
is a wearable device that will be running the latest version of the company’s mobile operating system,
iOS
.
Apple
‘s millions of devoted fans regularly cite the company’s security track record. In a recent
conference preview
we looked at various ways malware can persist on
OS X
, but the track record of
iOS
is stronger, with very few known malware cases. True, we recently published a
paper
on ‘AdThief’, which infected 75,000
iOS
devices, but these were all jailbroken.
However, in their paper, the
FireEye
researchers look at how
Apple
‘s enterprise program provides a surprisingly large attack vector.
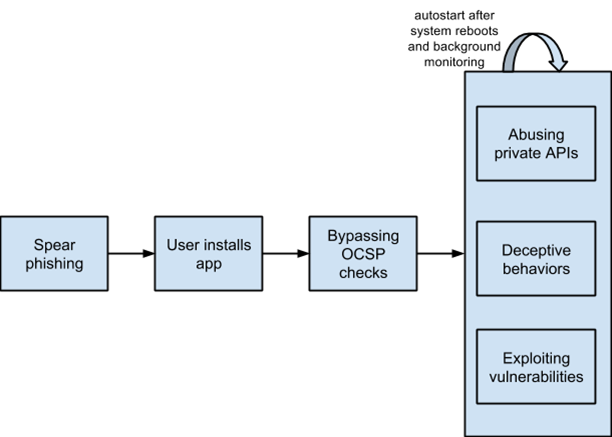
Targeted attacks against iOS through enterprise provisioning.
Though not perfect, with more than 100 rules,
Apple
‘s review process makes it difficult for malware to make it into the
App Store
. One of the restrictions is that non-
Apple
apps are not allowed to make use of ‘private APIs’.
Apple
is known to have banned apps that use these.
However, apps that are distributed through the ‘iOS Developer Enterprise Program’ – which allows a company to sign and distribute in-house apps – bypass this review process. Many vendors have used the enterprise program to distribute apps to the public.
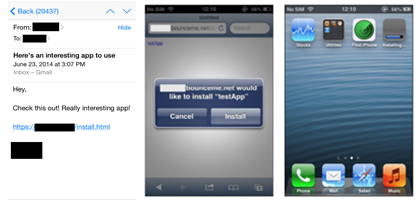
Using spear phishing to trick a user into installing an enterprise app.
Apple
may revoke an enterprise distribution certificate if it suspects abuse;
iOS
uses a protocol called OCSP to validate enterprise certificates. However, a well-known weakness in OCSP means that inability to contact the OCSP server isn’t considered a revocation – something an app can use during installation.
The fact that such apps have bypassed the review process allows them to automatically start after rebooting. Moreover, since private APIs are not intended to be used by app developers, they might not have been written as securely as the public APIs.
The researchers describe a number of vulnerabilities they found in private APIs that allow apps using them to monitor the phone’s user, making them ideal for those performing targeted attacks.
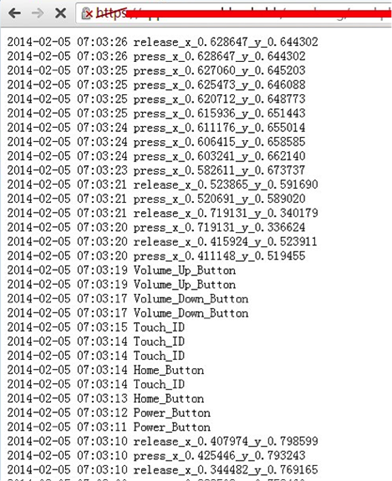
Monitoring a user’s activity in the background.
Finally, they point to a conundrum in the
iOS
security model, where security apps are not allowed to implement system-level protections, whereas malware can use enterprise provisioning to call private APIs.
Unsurprisingly, given the prevalence of mobile devices and the growing concern over their security, the VB2014
programme
includes various talks on mobile security, including several on
Android
and even
one presentation
on the
Tizen
platform.
Registration
for VB2014 is still open.
Posted on 12 September 2014 by
Martijn Grooten
Leave a Reply