30-month old vulnerability still a popular way to infect systems.
If all you have to worry about are zero-day vulnerabilities, you have got things pretty well sorted. Although it is true that sometimes zero-days are being used to deliver malware (such as the recent
use
of CVE-2014-4114 by the SandWorm group), in many cases even the more targeted attacks get away with using older, long patched vulnerabilities, exploiting the fact that many users and organisations don’t patch as quickly as they should — if at all.
CVE-2012-0158 is one such vulnerability.
Patched
in April 2012, the buffer overflow vulnerability exists in certain ActiveX controls and can be exploited via a malicious
Word
,
Excel
or RTF file.
Despite its age, the vulnerability continues to be used by various attack groups that all appear to operate in the Western Australian time zone. Examples of such groups include the ‘
Shiqiang Gang
‘ (as reported by
McAfee
), ‘
PLEAD
‘ (as reported by
Trend Micro
), ‘
NetTraveler
‘ (as reported by
Kaspersky
) and ‘
APT12
‘ (as reported by
FireEye
). Today,
G Data
published a
report
on ‘TooHash’, yet another operation that uses CVE-2012-0158 to infect victims.
Given a number of similarities between these attacks, it is possible that some of the groups behind it are indeed related. It is also possible that none of them are directly related, but that some use the same third-party to write the exploits. After all, not just ‘ordinary’ cybercrime is getting increasingly commoditized.
In either case, security researchers would do best not to assume CVE-2012-0158 a problem that is well behind us. Two papers published by
Virus Bulletin
last year may help you understand the technical details of the vulnerability.
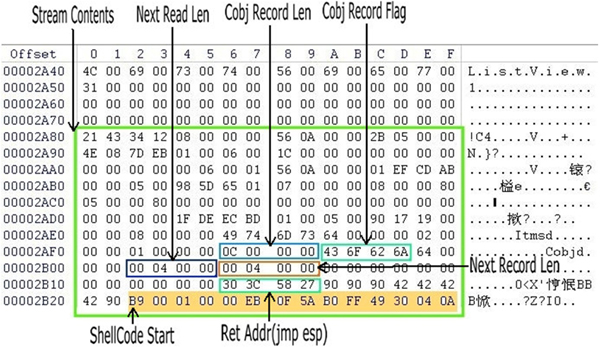
In May,
Fortinet
researcher Ruhai Zhang wrote an
article
on CVE-2012-0158, explaining the tricks used in exploits of the vulnerability to remain undetected by anti-virus software.
In a VB2013
conference paper
, Paul Baccas and Vanja Svajcer (then both at
Sophos
) took a deep look at RTF files containing an exploit for the vulnerability. A PDF of their paper can be downloaded
here
.
Posted on 31 October 2014 by
Martijn Grooten
Leave a Reply