Adobe ‘investigating reports’.
Vulnerable browser plug-ins are one of the most important infection vectors, which is why it is so important to keep them up to date. If you don’t, visiting a website infected with an exploit kit (a toolkit that attempts to exploit a number of vulnerabilities at once) could result in malware being dropped on the computer through a drive-by download.
The good news, however, is that keeping plug-ins fully patched usually suffices for the average Internet user: developers of exploit kits rarely ‘burn’ zero-days when targeting the general public.
But rarely isn’t the same as never. Pseudonymous security researcher Kafeine, who has long been keeping track of the latest developments in the world of exploit kits,
reports
that some instances of the ‘Angler’ exploit kit are using a hitherto unknown vulnerability in
Adobe
‘s widely used
Flash Player
.
Though few details are known at the moment, other security researchers have confirmed the finding, leading to speculation that a premium version of Angler might include the zero-day. Speaking to
Forbes
,
Adobe
confirmed
that it is investigating reports of the vulnerability.
The attack appears to target users of
Internet Explorer
on
Windows XP
through to
Windows 8
. Kafeine says the “bullet isn’t fired” on
Chrome
or on fully patched installations of
Windows 8.1
.
Many security firms were quick to point out that they would have blocked the exploit, either through heuristic detection, or because the Angler exploit kit was detected. Still, it might not be a bad idea to play safe and to enable click-to-play for
Flash
on websites.
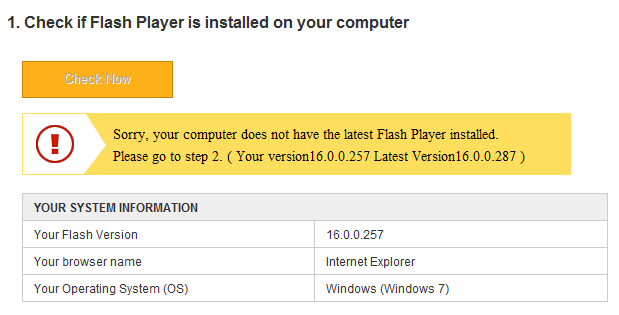
Interestingly, albeit somewhat confusingly, users of the latest
Flash Player
version 16.0.0.257 are
told
by
Adobe
to upgrade to version 16.0.0.287. This has been shipped with the latest version of
Google Chrome
, released yesterday, but is not yet available for download on
Adobe
‘s website. It is not clear whether the vulnerability is addressed in this update.
Posted on 22 January 2015 by
Martijn Grooten
Leave a Reply