Patch due next week as malvertising leads to Bedep trojan downloader.
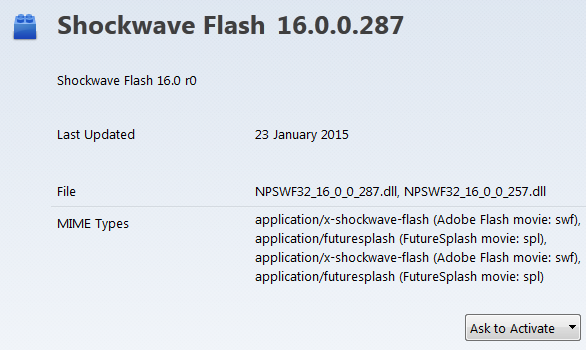
As the news of a zero-day vulnerability in
Adobe
‘s
Flash Player
actively being exploited reached the security community, the company made an out-of-band patch available on its website. It now appears that this update – version 16.0.0.287 – patches another vulnerability (
CVE-2015-0310
), but does
not
patch this latest flaw, which has been given CVE number
CVE-2015-0311
.
Adobe
says
that a patch for the latest vulnerability will be made available next week. It rates the vulnerability as critical and confirms that it is actively being exploited in the wild.
Even if you have the latest Flash Player version installed, making it click-to-play is very important.
Meanwhile, researchers at
ZScaler
provide
more details
on the use of the vulnerability in the Angler exploit kit. They say that two legitimate ad networks are being used to serve malicious ads, which redirect users to the exploit kit. This is then used to push the ‘Bedep’ trojan onto the victim’s system.
Bedep performs ad-fraud and click-fraud, thus making money for its owners by showing ads on the victim’s PC and faking clicks on such ads. Bedep is also a downloader, which could be used to download other, more harmful kinds of malware onto the machine.
The opportunities ad networks provide for malware authors was the subject of a paper
Bromium
‘s Vadim Kotov presented at
VB2014
. You can read Vadim’s paper
here
in HTML format, or watch the video of the presentation on our
YouTube
channel.
Posted on 23 January 2015 by
Martijn Grooten
Leave a Reply