Combination of anti-automation, anti-VM and anti-reverse engineering to make researchers’ lives harder.
Ever since the number of new malware samples became so large we could no longer list them in
Virus Bulletin
magazine, security researchers have been looking at ways to automate analysis. And ever since then, malware authors have been trying to find ways to make malware analysis in general, and automated analysis in particular, a lot harder.
Often, those techniques don’t appear in the malware itself but in packers, which are often specifically designed to hide the malware’s activities.
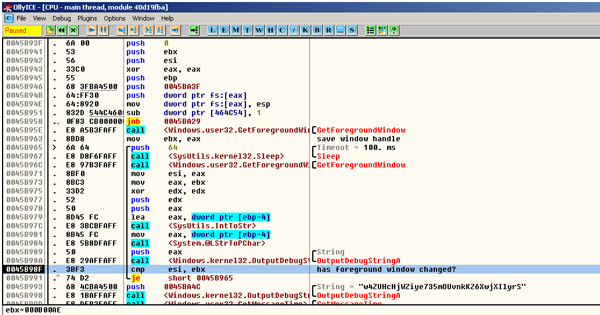
Checking the foreground window.
Today, we publish an article by
Symantec
researcher Ke Zhang in which he looks at three anti-analysis tricks applied by one such packer. In particular, the packer applies anti-automation to ensure it only runs when it is running on a real machine used by a human user, anti-VM which prevents it from running on a virtual machine, and anti-reverse engineering techniques to frustrate the lives of those analysing the packer.
Ke also showed how the packer was successful at hiding a malicious payload from various well known automation systems.
You can read the article
here
in HTML format or download it
here
as a PDF.
Leave a Reply