Israel’s
NSO Group
is in hot water following a
Haaretz
report that revealed that the company negotiated with the Saudi government on the sale of its spyware, leading the local branch of Amnesty International to
call
for the firm’s export licence to be revoked.
The list of targets of the group’s Pegasus spyware makes for some uncomfortable reading: it includes an
Emirati lawyer
, currently serving a ten-year prison sentence over tweets he sent, an
acquaintance
of the murdered Saudi journalist Jamal Khashoggi and, as
reported yesterday
, colleagues of a murdered Mexican journalist.
All of these cases were first reported by Toronto’s
Citizen Lab
. Based at the University of Toronto, the
Citizen Lab
is known for its work on the digital threats facing civil society – a subject on which two of the
Lab
‘s researchers, Masashi Nishihata and John Scott Railton, delivered a
presentation
at
VB2018
in Montreal.
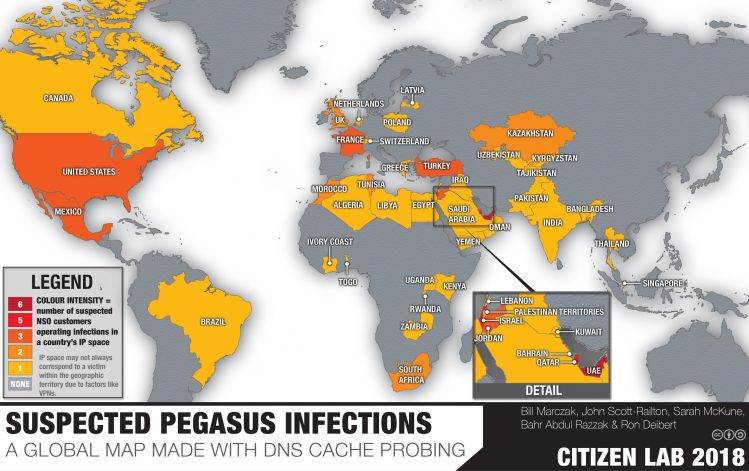
Global distribution of Pegasus spyware; from a September 2018
Citizen Lab report
.
However, while Masashi and John did begin their talk by discussing the Pegasus spyware and how it had targeted Canadian permanent resident and Saudi dissident Omar Abdulaziz (a friend of
Jamal Khashoggi
whose death, a day previously, wasn’t known about at the time of the presentation), their main argument was that such attacks using zero-days are actually the exception. Aptly titled ‘foreverdays’, their talk made the important point that malware targeting civil society tends to be “preventable, curable and technically boring” – the digital equivalent of tuberculosis rather than ebola.
Today we have uploaded the video of Masashi and John’s presentation to our
YouTube
channel
. They conclude their presentation by calling on the security industry to give civil society targets extra attention when they are found.
Leave a Reply