It is good practice not to mock or laugh at hacking victims. But when the victim is a company that itself is in the business of hacking and has a habit of selling its products and services to governments with dubious human rights records, few could help but smile at the irony.
This was the case when
Hacking Team
was
breached
in 2015 and details of its customers were published. Worse, from the Italian company’s point of view, was the fact that its source code, including several zero-day vulnerabilities, was leaked.
While several of the leaked vulnerabilities were being used by other attackers (a
2017 paper
by researchers from
F-Secure
, for instance, looked how this was done by the Callisto group),
Hacking Team
managed to
secure new funding
, and early in 2018 new activities were
spotted
in the wild by
ESET
researcher Filip Kafka.
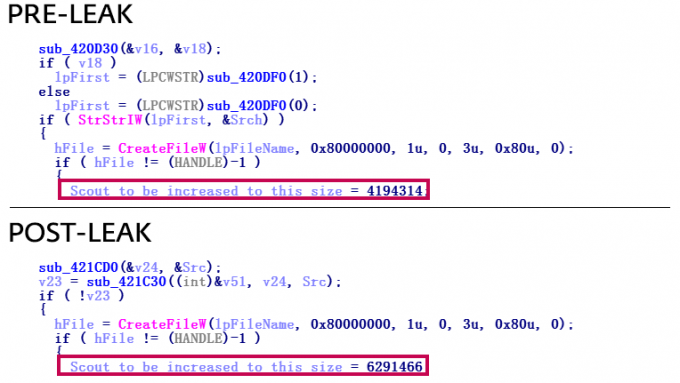
The size of Hacking Team’s ‘Scout’ first-stage malware changed between the pre- and post-leak versions.
Filip wrote a
technical paper
about these new activities, which he presented at VB2018 in Montreal last year. Today, we publish Filip’s paper in both
HTML
and
PDF
format and we have also uploaded the video of Filip’s presentation to our
YouTube
channel.
In Montreal, Filip’s presentation was followed by one from Masashi Nishihata and John Scott Railton of
The Citizen Lab
that we
previously published
. Their talk focused on digital threats to civil society, in which companies like
Hacking Team
play a dubious role, and thus nicely complements Filip’s technical presentation.
Have you analysed spyware used by governments? Or some other kind of digital threat? Why not submit an abstract for VB2019, which will take place in London, 2-4 October; the
call for papers
is open until 17 March.
Leave a Reply