PKPLUG is the name used by
Palo Alto Networks
’
Unit 42
team for a China-based threat actor engaged in cyber espionage. The actor uses both off-the-shelf and custom-made malware and some of its infrastructure overlaps with other threat groups.
The group’s activities were detailed in a VB2019 paper by
Unit 42
’s Alex Hinchliffe, who described the playbook of this long-standing adversary. (A shorter version was published around the same time in a
blog post
.)
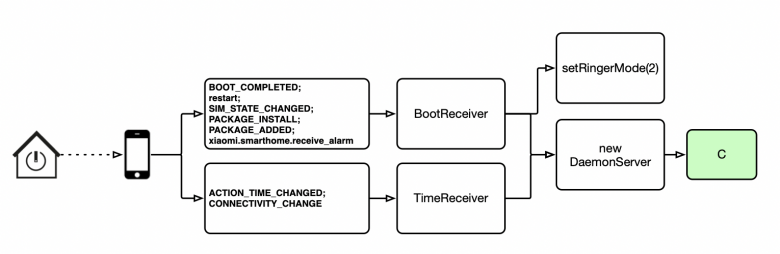
Automatic execution of the HenBox malware used by the PKPLUG adversary.
Today we publish Alex’s paper in both
HTML
and
PDF
format as well as the recording of his VB2019 presentation.

Pulling the PKPLUG: the adversary playbook for the long-standing espionage activity of a Chinese nation-state adversary
Read the paper (HTML)
Download the paper (PDF)
Have you carried out research that furthers our understanding of the threat landscape? Have you discovered a technique that helps in the analysis of malware?
The
Call for Papers
for VB2020 in Dublin is open! Submit your abstract before
15 March
for a chance to make it onto the programme of one of the most international threat intelligence conferences.
Leave a Reply