Apple
’s
MacOS
and
iOS
operating systems are often praised for their security. Yet vulnerabilities in both operating systems are regularly being found and exploited, especially by more advanced attackers.
In a paper presented at VB2019 in London,
Trend Micro
researchers Lilang Wu and Moony Li explained how researchers like them hunt for such vulnerabilities and how this hunting can be made both smarter and more automatic.
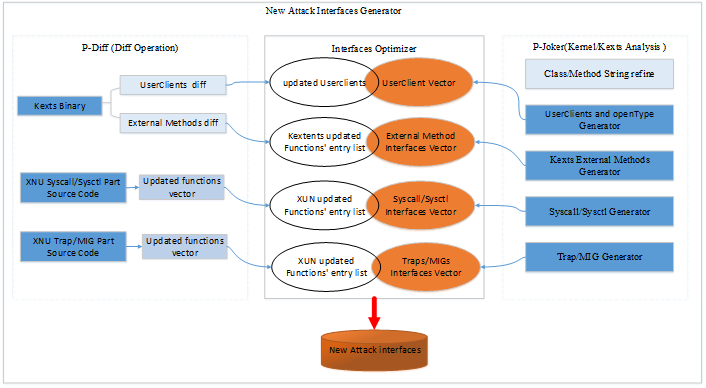
The reverse engineering solution for kernel and kextentions.
Today we publish the researchers’ paper in both
HTML
and
PDF
format as well as the recording of their VB2019 presentation.

Play fuzzing machine – hunting iOS and macOS kernel vulnerabilities automatically and smartly
Read the paper (HTML)
Download the paper (PDF)
Have you carried out research that furthers our understanding of the threat landscape? Have you discovered a technique that helps in the analysis of malware?
The
Call for Papers
for VB2020 in Dublin is open! Submit your abstract before
15 March
for a chance to make it onto the programme of one of the most international threat intelligence conferences.
Leave a Reply