Over the past few days, the Necurs spam botnet has increased its activity, sending large amounts of pump-and-dump spam, in which a cheap stock is pushed with the aim of making a profit for those behind the campaign. The
Dynamoo
blog
lists examples
of the various emails sent, while
Cisco
‘s
Talos
group provides
some context
to Necurs’ recent activity.
Necurs isn’t new: in 2014, Virus Bulletin published a series of articles on the malware by
Microsoft
researcher Peter Ferrie (
1
,
2
,
3
). In fact, Necurs, which
used to
spread through exploit kits, actually stopped spreading some time ago, meaning that the infections involved in the recent activity will have existed for a long time (thanks to
MalwareTech
for confirming this).
It therefore doesn’t come as a surprise that most of the Necurs spam we see comes from countries like Vietnam, India and Indonesia, where for understandable economic reasons, computer hygiene isn’t on par with that in more advanced economies.
The spam itself isn’t particularly advanced either, and no effort has been made to bypass spam filters. The emails don’t use DKIM, and the MAIL FROM addresses don’t appear to have been chosen with the aim of avoiding SPF fails. We looked at one Necurs spam campaign that started this morning and found that most of the spam filters we are currently testing
in our lab
blocked all of the messages; in fact, all but a handful of IP addresses from which the spam was sent were listed on prominent IP blacklists. It is thus fair to say that very few of the emails in this campaign would have been seen by a human being.
But maybe that doesn’t matter for those who hired Necurs to send out the spam: all they would have cared about is that some people would act on the spam and buy the stock, thus increasing its value. Or maybe that trading algorithms scouring the Internet would notice an increase in mentions of the stock and buy it, thus increasing its value. Whatever the reason, the value of the stock
did indeed rise
.
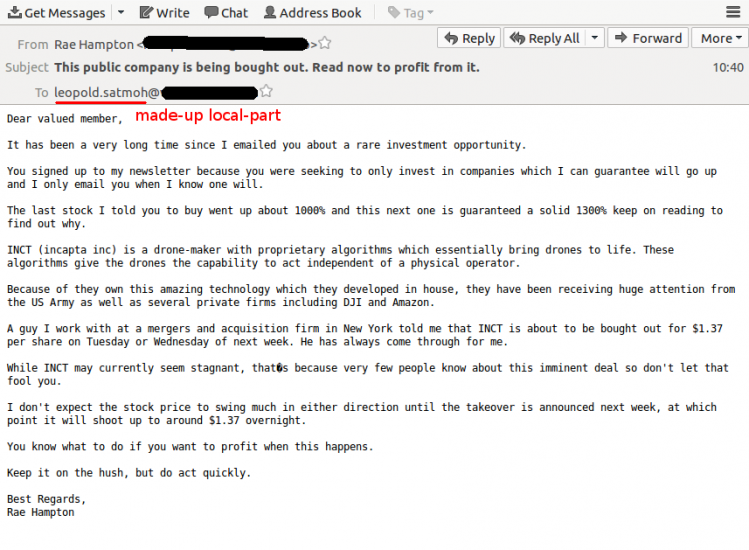
That doesn’t mean that Necurs’ clients don’t have a reason to complain about the service provided: more than half of the Necurs spam we saw in this particular campaign was sent to email addresses with a made-up local-part, likely a method used by the botnet owners as an easy way to increase numbers. Things change quickly in the global threat landscape, but one thing remains the same: in 2017, you still can’t trust spammers.
In the meantime, such campaigns provide interesting possibilities for malware researchers.
I’m wondering about legality of knowingly buying into someone else’s pump & dump. I monitor Necurs, so i get the mails before anyone else.
— MalwareTech (@MalwareTechBlog)
March 21, 2017
Leave a Reply