There are many good reasons to criticize
Facebook
for its collecting of our personal data, but the company also deserves credit for being at the forefront when it comes to online security.
The company has long had a generous
bug bounty program
, can send
PGP-encrypted
notifications, and has even set up a
.onion version
of its website. Now the company has
made it easy
to determine whether a security notification that claims to have come from
Facebook
really was sent by its servers, or whether it might actually be a phishing or otherwise malicious email.
I’ve never been very happy with the advice that you should only open emails that you can be certain are genuine, and that you should check the links before clicking on them: it has resulted in phishers trying harder to make their emails and the links within them look genuine – at least to an untrained eye. A much better piece of advice is to browse directly to the site from which the email claimed to come, without clicking any links in the email, and see if you are still prompted to do whatever was apparently so urgent.
Unfortunately, it is not easy for a user be sure that the absence of any notification means that an email was fake. In fact, I would be surprised if there weren’t many websites that send genuine security notifications by email without notifying you about them in your account.
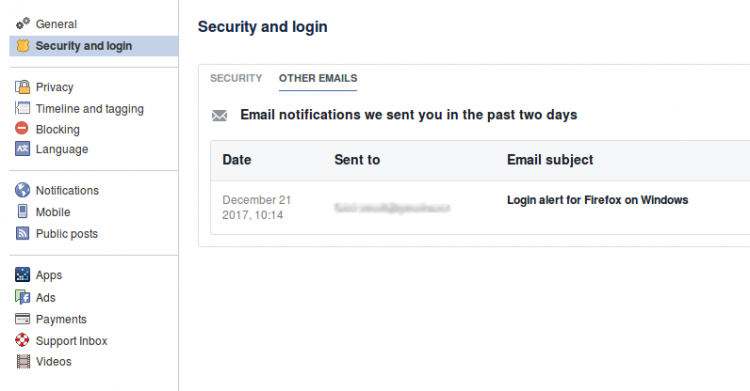
To address this problem,
Facebook
‘s security settings now show all recent emails the company has sent you: if an email you have received isn’t listed there, it didn’t come from
Facebook
. And if it is listed there, it almost certainly did come from
Facebook
and means the link within it is safe to be clicked.
Of course, this shouldn’t stop users from setting up two-factor authentication. But it does make it really easy for the recipient to ask the perceived sender: did you really send this email? Let’s hope other widely phished sites will follow
Facebook
‘s example.
Leave a Reply