Cisco Talos
researchers Warren Mercer and Paul Rascagnères recently
discovered and analysed
‘GravityRAT’, an advanced Remote Access Trojan (RAT) that appears to have been used in targeted attacks against organizations in India. Analysis of this piece of malware gives an interesting insight into the current state of malware development.
The malware is delivered through a malicious
Microsoft Office
document, likely sent via email, which is a common way for both targeted and opportunistic malware to infect devices. The authors appear to have uploaded early versions of the malicious document to
VirusTotal
, to measure the detection of their code by a range of anti-virus products.
In general, using
VirusTotal
in this way gives a malware author only limited insight into whether a piece of malware will be blocked:
VirusTotal
uses static anti-virus scanners and thus uploading a malicious file to the service can only help its author understand whether it will be detected as malicious, not whether the malware will actually be allowed to run. On top of a static detection engine, endpoint security software typically includes various layers of protection that aim to prevent both known and unknown malware from running.
For a malicious document, however, static detection is important in determining whether it will bypass an email security product; if the file is not detected, it is more likely to be able to bypass such security measures – especially if the document is sent only in small quantities, thus not triggering anti-spam detectors in such products.
If the file is opened, and if macros are enabled by the user, the actual payload will be downloaded.
The GravityRAT Remote Access Trojan (or Tool) is noteworthy for the fact that is uses no fewer than seven techniques to detect whether it is running inside a virtual machine.
A lot of today’s malware is ‘VM-aware’, and when it detects that it is being run inside a virtual machine (and is thus likely to be being analysed by a human or a malware-detection sandbox), it either terminates or changes its behaviour. Common techniques for detecting a virtual machine environment include looking for traces of the hypervisor left on the virtual machine, checking the computer name, and checking the number of CPU cores – all of which GravityRAT does.
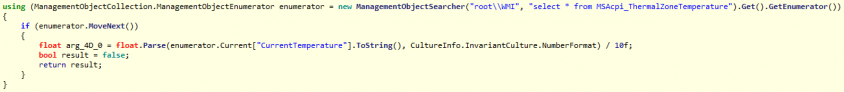
But it also uses a novel technique where it requests the CPU temperature – a feature not commonly supported by hypervisors. These will then respond ‘not supported’, thus revealing that the malware is probably not being run on a real machine.
For many years, there has been a continuous cat-and-mouse (cat-and-rat?) game between malware writers and the developers of virtual machines and sandboxes. Analyses like this help the latter update their tools and thus force the malware authors to work even harder.
Warren and Paul
spoke
at VB2017 last year and will be back at VB2018 in Montreal, to
discuss
the ‘Olympic Destroyer’ malware. Registration for
VB2018
will open very soon.
Leave a Reply