Static analysis of malware is usually “done by a person (a security analyst) who will stare at one binary code for hours, searching for patterns – the signatures,” writes Thaís Moreira Hamasaki in her VB2018 paper.
To make the analysis process faster and more effective, analysts tend to use various tools and techniques. One lesser known technique that is becoming increasingly popular among malware analysts is constraint programming, which gives insight into the conditions necessary for the execution to take specific branches.
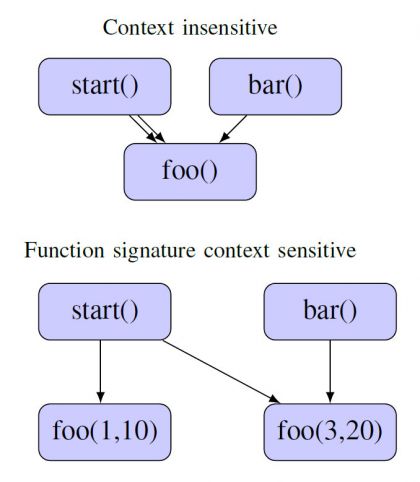
Example of context sensitivity for a simple program.
In her detailed VB2018 paper, Thaís (who was then at
F-Secure
) presented an overview of constraint programming and explained how it can be applied to the analysis of (potentially) malicious binaries. Today we have published Thaís’ paper in both
HTML
and
PDF
format. We have also uploaded the video of her presentation to our
YouTube
channel.
Do you know of a new or little known tool that can aide in the manual analysis of malware? Why not submit an abstract for VB2019, the upcoming Virus Bulletin conference that is to take place in London, 2-4 October. The
Call for Papers
closes on 17 March.

Leave a Reply