Half a decade ago, breaches of point-of-sale (POS) systems were a real plague, especially in North America, with the 2013
Target
breach
perhaps the best known example.
Though credit card theft through POS hacks hasn’t completely disappeared, today’s skimmers largely act online, using JavaScript to insert skimmers into websites’ payment pages.
The more than a dozen different groups behind these breaches are referred to by the umbrella term ‘Magecart’, a name first used by
RiskIQ
and made popular through a 2016
joint report
by
RiskIQ
and
Flashpoint
. Different groups use different tactics, from targeted attacks against big websites to automatically scanning for known CMS vulnerabilities, to compromising third-party JavaScript code loaded on such websites.
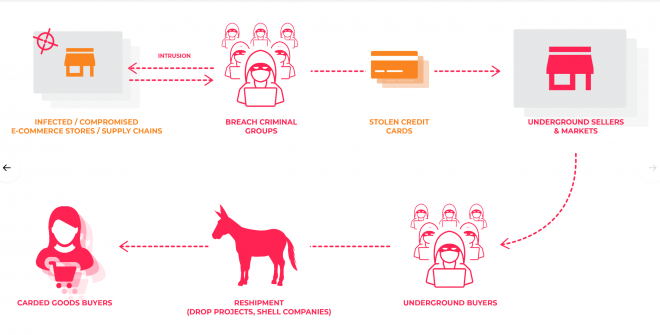
A rich underground economy exists around all the different steps needed to monetize a breach.
At
VB2019
in London,
RiskIQ
researcher Yonathan Klijnsma will present a
paper on Magecart
, in which he discusses the history of web skimmers and profiles six Magecart groups to provide a good overview of the different modi operandi of the various groups.
Don’t forget to
book your ticket for VB2019
to see Yonathan and dozens of other speakers discuss the latest trends in threat intelligence. And if you are quick, the
call for last-minute papers
for the conference remains open for submissions until the end of this weekend!

Leave a Reply