Though still relatively new (the
first VB conference paper
on
Android
malware was presented in 2011), malware targeting the
Android
mobile operating system has evolved quickly, in terms of both quantity and quality. Many of the characteristics of desktop malware are now also seen in
Android
malware – for example, the use of anti-analysis techniques, and the use of libraries for such techniques, is a sign of the commoditization of
Android
malware.
One such library was found in more than 5,000
Android
malware samples, including newer variants of the
Chamois
ad fraud malware. In reference to its many layers,
Google
researcher Maddie Stone named the library ‘WeddingCake’.
In a
paper
presented at VB2018 in Montreal, Maddie took apart the library and its many layers – an analysis which will be helpful not just to those who come across WeddingCake in their research, but also for those analysing similar libraries.
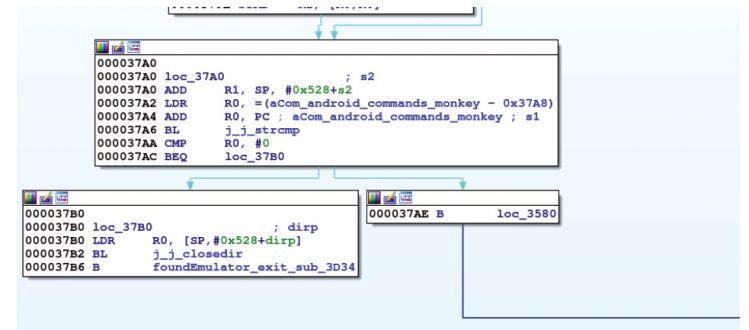
The library checks if the
Monkey
application is running, which would indicate it is running inside an emulator.
Today, we published Maddie’s paper in both
HTML
and
PDF
format. We have also uploaded the video of Maddie’s talk to our
YouTube
channel.
A call for papers for
VB2019
(London, 2-4 October) will open this week. Sponsor/partner opportunities for VB2019 – the most international threat intelligence conference – are now
available
.
Leave a Reply