Walking around the
RSA
show floor last week, it was clear that the Internet of Things, or IoT, is a hot topic in security.
Indeed, the number of connected devices continues to grow and new IoT botnets continue to be discovered, with
Saikin
and
Hajime
being two of the most recent examples.
It is important to realise that most of these IoT botnets consist of routers (Mirai, which included IP cameras, is a notable exception). There are two fundamental, and rather obvious, differences between routers and other kinds of connected devices.
The first is that routers are
supposed
to be connected to the Internet. One can have a discussion about whether it is a good idea to connect a fridge or a coffee maker to the Internet, but for a router, the whole point is to connect it to the Internet.
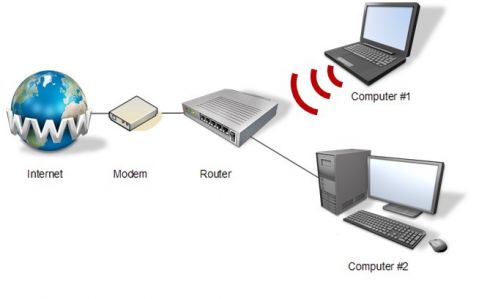
Placement of the router in the network. (From the VB2017 paper
The router of all evil: more than just default passwords and silly scripts
by Himanshu Anand & Chastine Menrige.)
The second is that security issues for most IoT devices are mitigated by them being behind a NAT, and thus not directly reachable from the Internet. A router is typically connected directly to the Internet – in fact, routers are gateways to the aforementioned NATs.
What most routers do have in common with other kinds of IoT devices is that their software tends to be weak and poorly maintained, and that if the device even allows for security patches to be installed in the first place, users often don’t bother. Indeed, a recent
survey
found that more than half of Internet users had never made a change to their router, and hadn’t even changed the default Wi-Fi password.
And this is why I feel optimistic about a new trend in which security companies are producing their own routers (or in some cases, devices that sit directly behind routers). Firstly, we can expect such routers to be designed with security in mind and thus both to have fewer vulnerabilities and, more importantly, to include the ability to install security patches automatically.
Secondly, while NATs do mitigate some of the risks that come with IoT, they aren’t perfect and are likely to become less effective as IPv6 becomes more prevalent. A security-focused router has the ability to block malicious traffic and thus prevent devices from being infected with malware and, if they do get infected, prevent them from reaching out to C&C servers.
None of this should be a reason for device manufacturers to ignore security in the design process. But getting the IoT industry to take security more seriously is likely to be a long process. In the meantime, anything we can do to mitigate the risks is very welcome.
Leave a Reply