Micky Pun and Neo Tan analyse the banking trojan that is best known for spreading through Skype.
Since the close of the VB2014 conference in Seattle in October, we have been sharing VB2014 conference papers as well as video recordings of the presentations. Today, we have added ‘Caphaw – the advanced persistent pluginer’ by Fortinet researchers Micky Pun and Neo Tan.
Caphaw (also known as Shylock) is a bit of a rarity among today’s botnets: its source code hasn’t been leaked and the malware has never been offered for sale on underground forums, suggesting that the same group of people wrote the code and maintained the botnet.
Other than that, the banking trojan shows many similarities with other modern malware families: from anti-analysis techniques to the possibility of extending the malware by using plug-ins.
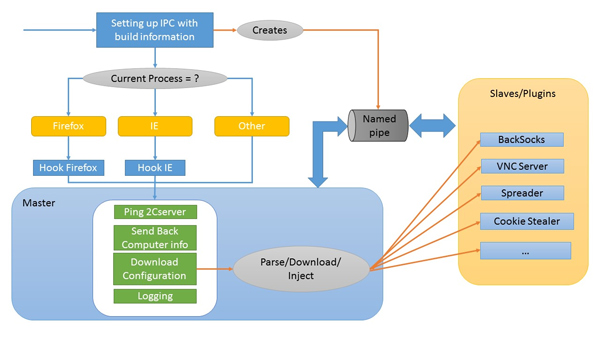
An overview of Caphaw; click for larger.
Today, we publish a VB2014 paper from
Fortinet
researchers Micky Pun and Neo Tan, in which they take a close look at Caphaw. They look at how the malware communicates with its command and control server and at the malware’s configuration file as well as at its various plug-ins, most famous among which is one that helps the malware spread through
Skype
chats.
The story of Caphaw (and Micky and Neo’s presentation) ends on a positive note: in June 2014 the botnet disappeared off the radar. It seems that this was thanks to a
coordinated action
led by the UK’s National Crime Agency against the botnet’s infrastructure. However, no arrests were made.
You can read Micky and Neo’s paper on Caphaw
here
in HTML-format, or download it
here
as a PDF (no registration or subscription required). We have also uploaded the presentation to our
YouTube
channel.
Those interested in the
Skype
module should also read an
article
Micky and Neo’s colleague Raul Alvarez wrote for
Virus Bulletin
two years ago, in which he looks at this module. Caphaw/Shylock was also studied in
another VB2014 paper
, by
Sophos
‘s James Wyke, who looked at decoy behaviour performed by malware upon sandbox detection.
Posted on 27 February 2015 by
Martijn Grooten
Leave a Reply