Malware remains present on infected machines; 2012 Virus Bulletin paper worth studying.
A coordinated action from
Anubisnetworks
,
Microsoft
and
Symantec
, together with
Europol
has done serious damage to the infrastructure behind the ‘Ramnit’ botnet.
Ramnit is one of those botnets that lurk in the background of the Internet. Its infections mainly occur in countries where the security community tends to have less visibility, with the top three infected countries being India, Indonesia and Vietnam. It is believed to have infected more than 3 million computers in total, and the number of infected machines at the time of the takedown remained fairly high at around 350,000.
Ramnit stole banking credentials, cookies and other kinds of personal information from the machines it infected, while it could also open backdoors and steal FTP credentials. The latter were then used by the malware to propagate further.
While the botnet’s current infrastructure has been taken down, the malware remains present on the machines. Time will tell whether the botnet owners will be able to revive it, but for now they have been delivered a significant blow.
In November 2012,
Virus Bulletin
published an
article
by
Fortinet
researcher Chao Chen, who thoroughly analysed Ramnit and all its modules. Given that the infected machines haven’t been cleaned up, the article is well worth studying for anyone wanting a full understanding of how the malware operates.
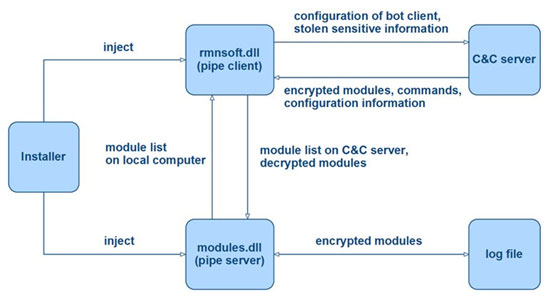
Ramnit, like many modern pieces of malware, is highly modular. This diagram shows the process used to download modules.
Posted on 26 February 2015 by
Martijn Grooten
Leave a Reply