Chun Feng and Elia Florio look at exploits targeting domain memory opcode in Adobe Flash.
In the weeks running up to
VB2014
(the 24th Virus Bulletin International Conference), we are looking at some of the research that will be presented at the event. Today, we look at the paper ‘
Ubiquitous Flash, ubiquitous exploits and ubiquitous mitigation
‘, by Microsoft researchers Chun Feng and Elia Florio.
In a
recent VB2014 preview
, we looked at a paper that shows how advertisements on websites provide many opportunities for those trying to get their malware installed on many computers. Most of these advertisements attempt to exploit vulnerabilities in
Adobe Flash Player
.
In their paper, Chun and Elia take a close look at two Flash vulnerabilities, which are both caused by flaws in
Flash Player
‘s implementation of domain memory opcode, and which have both been used to spread malware, and a third case of an
IE
vulnerability exploited with some help from specific
Flash Player
techniques.
The first vulnerability is
CVE-2013-5330
. It allows an attacker to craft an SWF file that can read/write to an arbitrary memory location – something that makes such an attack rather powerful as exploits go.
More than two months after the vulnerability was patched, the pseudonymous blogger ‘Kafeine’
found
it being used in the wild in an exploit kit served on ‘high rank websites’. The paper describes in detail how the sample used the exploit to drop malware (W32/Lurk) on a vulnerable system.
The second vulnerability is
CVE-2014-0497
and can be considered a real child of the former: it was introduced with the patching of CVE-2013-5330, making relatively few
Flash Player
versions vulnerable. It was found being exploited in the wild in February this year, after which
Adobe
released an out-of-band patch.
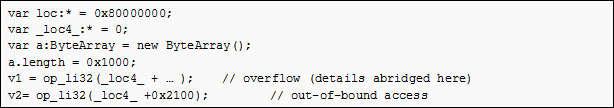
The exploit code snippet for CVE-2014-0497.
In the third case,
CVE-2014-0322
, Flash functioned as a ‘helper’ to exploit a vulnerability in a web browser, more particularly
Internet Explorer
. This is possible, because
IE
and the
Flash Player
plug-in share the same address space. The paper describes how this was used to allow an attacker to access an arbitrary memory location for read and write actions.
There is good news, however, as both
Adobe
and
Microsoft
have introduced mitigations that should make exploitation of such vulnerabilities harder in the future. The paper describes how
Microsoft
‘s
Enhanced Mitigation Experience Toolkit
(
EMET
) would have blocked both exploits using multiple mitigations. Those who saw Jarno Niemelä’s
VB2013 presentation
(which can be watched
here
) will know that
EMET
is very effective against many new exploits.
Still, more can be done. The paper finishes by urging
Adobe
to release a byte-code-level SWF debugger to make the analyst’s life easier.
VB2014 takes place next week in Seattle.
Registration
for VB2014 is still possible.
Posted on 19 September 2014 by
Martijn Grooten
Leave a Reply