Axelle Apvrille and Ruchna Nigam look at both off-the-shelf products and custom obfuscation techniques.
After a relatively slow start, in recent years mobile malware has really taken off. In many ways, mobile malware has followed the same path as taken by malware targeting desktop PCs. We have seen mobile adware, spyware, fake anti-virus, banking trojans, ‘police ransomware’ and recently even file-encrypting ransomware.
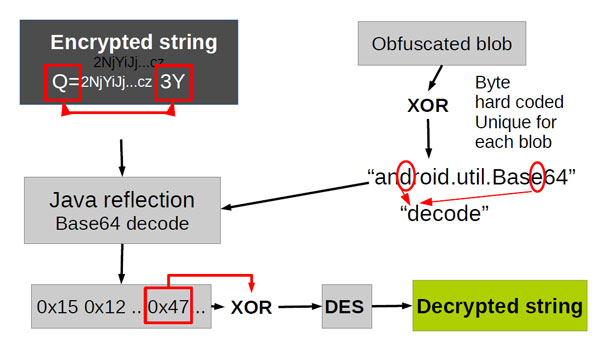
As with desktop malware, mobile malware commonly uses obfuscation to hide its payloads from analysts’ eyes and to make detection by security products more difficult. But, as the underlying operating systems are different, so are the obfuscation techniques used.
Today, we publish a paper by Axelle Apvrille and Ruchna Nigam, two researchers from
Fortinet
in France, on obfuscation in
Android
malware. In the paper, they analyse both off-the shelf obfuscation tools and custom obfuscation techniques written by malware authors. They also look ahead at how obfuscation might develop in the future, and at how such future techniques may be detected.
As of this month, all papers published through
Virus Bulletin
are available free of charge. You can download this paper
here
in HTML format, or
here
as a PDF (no registration required).
If you are interested in
Android
malware, you may also like the two-part analysis (
1
,
2
) of ‘Zitmo’ (‘Zeus-in-the-Mobile’), written by Axelle with her colleague Kyle Yang in 2011.
Posted on 02 July 2014 by
Martijn Grooten
Leave a Reply