Researchers initially believed Google warning was a false positive.
For a few days this week, the popular
php.net
website was serving malware to some of its visitors and was doing so in a stealthy way that initially confused researchers.
There may be thousands and possibly millions of malicious websites on the Internet, but when you want to, it isn’t always trivial to get infected by a compromised site that is spreading malware.
Attackers apply a number of methods to avoid their drive-by downloads being detected by security researchers and bots scanning the web for vulnerabilities. They also tend to avoid serving the malware twice to the same IP address: because a lot of malware authors get paid through affiliate schemes for the number of machines they infect, there is little point in them trying to serve the malware to the same address more than once.
We saw yesterday that this actually matters in practice, after
Google
had started flagging
php.net
as malicious. The official website for the web programming language PHP not only hosts a vast amount of documentation, it also serves the PHP source code.
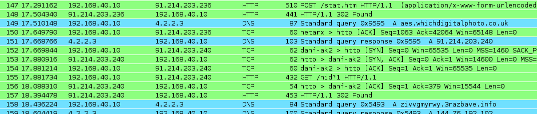
Many researchers were not able to replicate the issue and it was believed that it was a false positive at first. However, someone
posting
on the
Hacker News
website did claim that they had been served a malicious JavaScript file – and they posted the contents. When
Barracuda
helpfully
posted
a
pcap
file that recorded another visit to
php.net
on its blog, it turned out that
Google
had been right all along.
Interestingly, the JavaScript from the two sources is different: both are heavily obfuscated pieces of the same code that injects an iframe into the website. By not using the same piece of code, the attackers made it harder for the compromise to be blocked through a signature.
It also shows that the attackers didn’t simply modify the contents of a static file, as
php.net
initially thought
, but managed to compromise the web server itself. This confusion is understandable though: web-based malware
can be rather stealthy
.
The injected iframe served what, according to
Kaspersky
‘s
Fabio Assolini
, was the ‘Magnitude’ exploit kit. The exploit kit was being served through subdomains of a number of related UK websites that probably had their DNS compromised; the domains all pointed to servers in Moldova.
It is unclear how many users have been infected, but in an updated statement,
php.net
says
that the site had been serving malware for several days. One might expect that most of those who visit a site about a programming language would have their browser running the latest security patches – but given its top 250 place in
Alexa
‘s ranking, there will undoubtedly have been many visitors who did not, and who got themselves infected through the visit.
The site says it has now found two servers that were compromised and has solved the issue, although it is still not clear how the initial compromise took place. We hope that once the
php.net
team find out, they will share this information with the community. Thankfully, the attackers did not make any changes to the actual PHP source code.
A full write-up of the story, including some quotes by me, can be found at
Ars Technica
here
.
Trustwave
‘s Ryan Barnett wrote a detailed analysis of the infection on the
SpiderLabs
blog
here
.
Posted on 25 October 2013 by
Martijn Grooten
Leave a Reply